Network Access Protection (NAP) is a security technology introduced in Windows Server 2008 which can be deployed on computers running Windows Server 2008 R2 and Windows 7 or later operating systems (but not Windows 10). NAP includes client and server components that allow you to create and enforce health requirement policies that define the required software and system configurations for computers that connect to your network. NAP enforces health requirements by inspecting and assessing the health of client computers, limiting network access when client computers are deemed noncompliant, and remediating noncompliant client computers for unrestricted network access. NAP also provides ongoing health compliance enforcement while a compliant client computer is connected to a network.
NAP enforcement occurs at the moment when client computers attempt to access the network through network access servers, such as a VPN server running Routing and Remote Access, or when clients attempt to communicate with other network resources. NAP enforces health requirements for the following:
- Internet Protocol security (IPsec)-protected communications
- Institute of Electrical and Electronics Engineers (IEEE) 802.1X-authenticated connections
- Virtual private network (VPN) connections
- Dynamic Host Configuration Protocol (DHCP) configuration
- Terminal Services Gateway (TS Gateway)
NAP can interoperate with any vendor software that provides SHAs and SHVs or that recognizes its published API set. NAP helps provide a solution for the following common scenarios:
- Check the health and status of roaming laptops (for the endpoint device without malware protection).
- Ensure the health of desktop computers.
- Verify the compliance and health of computers in remote offices.
- Determine the health of visiting laptops.
- Verify the compliance and health of unmanaged home computers.
- Update with the latest operating system patches
The following role services can be installed with this role.
Network Policy Server (NPS)
NPS is a centrally manage network access through a variety of network access servers, including RADIUS-compliant 802.1X-capable wireless access points, VPN servers, dial-up servers, and 802.1X-capable Ethernet switches. In addition, you can use NPS to deploy secure password authentication with Protected Extensible Authentication Protocol (PEAP)-MS-CHAP v2 for wireless connections. NPS also contains key components for deploying NAP on your network.
Health Registration Authority (HRA)
HRA is a NAP component that issues health certificates to clients that pass the health policy verification that is performed by NPS using the client SoH. HRA is used only with the NAP IPsec enforcement method.
Host Credential Authorization Protocol (HCAP)
HCAP allows you to integrate your Microsoft NAP solution with Cisco Network Access Control Server. When you deploy HCAP with NPS and NAP, NPS can perform client health evaluation and the authorization of Cisco 802.1X access clients.
NPS supports three types of policies:
- Connection requests: Determine general rules for requests from RADIUS clients, such as whether specific requests are handled by the NPS or proxied to another RADIUS server.
- Network policies: Define how connection attempts are either authorized or rejected.
- Health policies: Define health rules that must be met in order to connect.
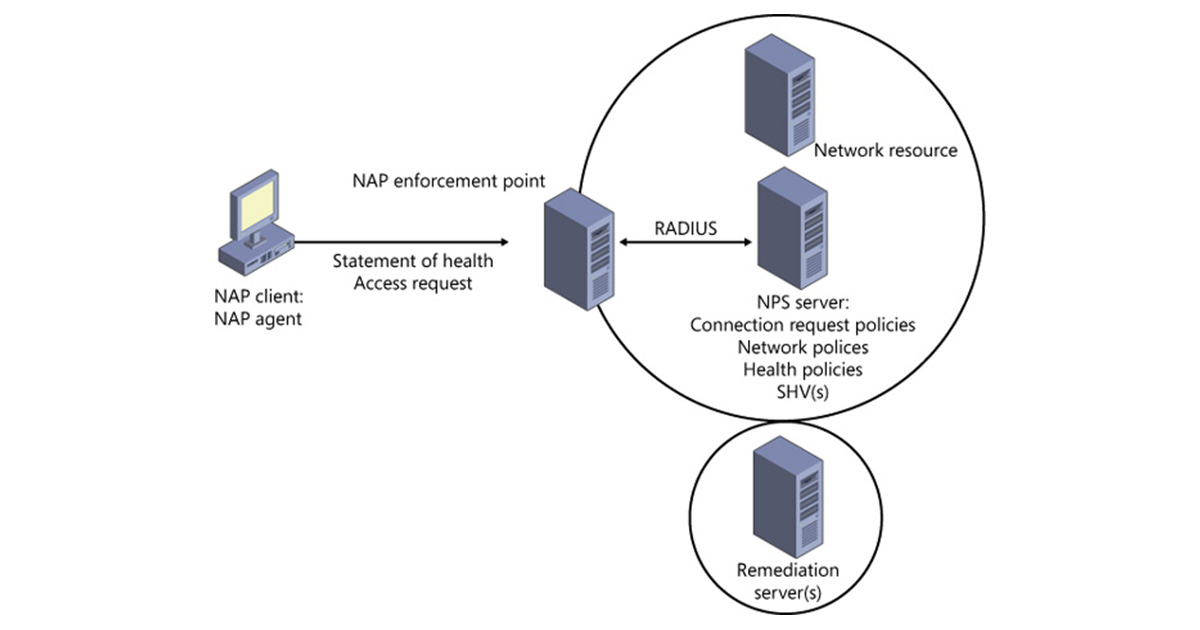
How does NAP work:
During login, a NAP client reports system status to a NAP enforcement device such as a switch, VPN server, DHCP server, or other services. The NAP enforcement device reports the endpoint’s health to a Network Policy Server under Windows Server 2008 or Windows Server 2008 R2. The NPS evaluates the status against requirements established by the system administrator.
If the NAP client logging in meets the NPS requirements, it will be allowed to log into the corporate network normally. If the NAP client trying to log into the corporate network doesn’t comply with NPS requirements, the client can be blocked or placed on a network with restricted access until its health can be corrected by the user or through a remediation server containing the required patches, signatures or other content. Once the client’s health is updated and compliant, a new request for a health check can be made.